Azure -Serverless web application -Architecture
Today we will discuss the serverless web application, with the help of reference architecture. The application serves static content from Azure Blob Storage and implements an API utilizing Azure Functions. The API reads data from Cosmos DB and returns the results to the web app.
The term serverless has two distinct but cognate denotements:
Backend as a service (BaaS): Back-end cloud services, such as databases and storage, provide APIs that enable client applications to connect directly to these services.
Functions as a service (FaaS): In this model, a "function" is a piece of code that is deployed to the cloud and runs inside a hosting environment that plenarily abstracts the servers that run the code.
The conception is that developers and DevOps personnel don't require to deploy, configure, or manage servers. This reference architecture fixates on FaaS utilizing Azure Functions, although serving web content from Azure Blob Storage could be an example of BaaS.
Functions are executed when an external trigger occurs, such as an HTTP request or a message arriving on a queue. This makes an event-driven architecture style natural for serverless architectures.
The architecture consists of the following components:
Azure CDN: Azure Content Distribution Network (CDN) is a global CDN solution for distributing high-bandwidth content. With Azure CDN, we can cache static objects loaded from Azure Blob storage, a web application, or any publicly accessible web server, by utilizing the most proximate point of presence (POP) server. Azure CDN can withal expedite dynamic content, which cannot be cached, by leveraging sundry network and routing optimizations.
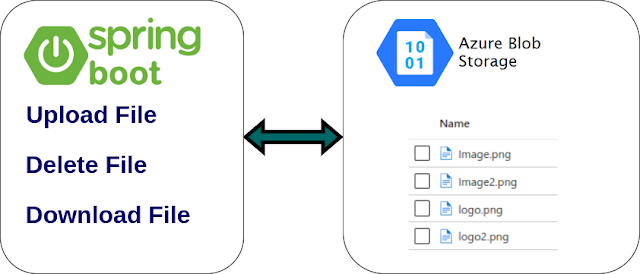
Azure Blob Storage: Static web content, such as HTML, CSS, and JavaScript files, is stored in Azure Blob Storage and served to clients by utilizing static website hosting. All dynamic interaction transpires through JavaScript code making calls to the back-end APIs. There is no server-side code to render the web page. Static website hosting fortifies index documents and custom 404 error pages.
Azure Functions: Azure Functions are the individual functions engendered in a Function App. Every Function can be invoked utilizing the configured trigger. The Azure portal provides the capabilities to engender, manage, monitor, and integrate inputs & outputs of the Azure Functions.
API Management: APIM avails organizations to publish APIs to external, partner, and internal developers to unlock the potential of their data and services. API Management provides the core competencies to ascertain a prosperous API program through developer engagement, business insights, analytics, security, and protection.
Cosmos DB: Cosmos DB is a multi-model database service. For this scenario, the function application fetches documents from Cosmos DB in replication to HTTP GET requests from the client.
Azure Active Directory: Users sign into the web application by utilizing their Azure AD credentials. Azure AD returns an access token for the API, which the web application uses to authenticate API requests.
Azure Monitor: Azure Monitor accumulates performance metrics about the Azure services deployed in the solution. By visualizing these in a dashboard, we can get overtness into the health of the solution. It withal amassed application logs.
Azure Pipelines: Pipelines is a continuous integration (CI) and continuous delivery (CD) service that builds tests, and deploys the application.







Comments
Post a Comment