AWS Secret Manager Service as application properties with Spring boot
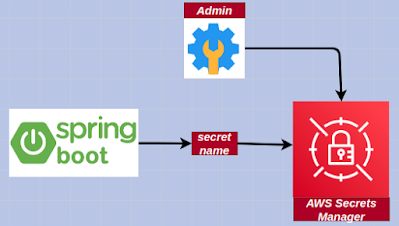
Secrets Manager enables us to supersede hardcoded credentials in our code, including passwords, with an API call to Secrets Manager to retrieve the secret programmatically . These avails ascertain the secret can't be compromised by someone examining our code, because the secret no longer subsists in the code. Withal, we can configure Secrets Manager to automatically rotate the secret for us according to a designated schedule. This enables us to supersede long-term secrets with short-term ones, significantly abbreviating the peril of compromise. Overview 1. The admin creates a new secret in AWS Secrets Manager 2. A Spring Boot application uses the secret name to access the secrets stored in AWS Secrets Manager Step 1: Create & Store secrets in AWS Secret Manager. Use the AWS Console to create and store a new secret in AWS Secrets Manager. Link Step 2: Add the below dependency to the pom.xml file. <dependency> <groupId> com.amazonaws </groupId> <art